Difference between revisions of "Training: vLAN"
m |
|||
| Line 39: | Line 39: | ||
Switch setup: The port the PBX is going to be plugged into needs to be a member of the voice vLAN UNTAGGED (the pbx will be sending and receiving untagged traffic in this configuration). The ports that will have phones plugged into them will need to be members of the data vALN untagged, and the voice vLAN TAGGED, as the phone will be sending/receiving tagged packets, while the computer (if any), plugged into each phone, will be sending its data network traffic as UNtagged. | Switch setup: The port the PBX is going to be plugged into needs to be a member of the voice vLAN UNTAGGED (the pbx will be sending and receiving untagged traffic in this configuration). The ports that will have phones plugged into them will need to be members of the data vALN untagged, and the voice vLAN TAGGED, as the phone will be sending/receiving tagged packets, while the computer (if any), plugged into each phone, will be sending its data network traffic as UNtagged. | ||
| + | |||
| + | The ports that are members of vLAN 10, whether tagged or untagged, can communicate with each other. Ports NOT members of vLAN 10 at all can NOT communicate with vLAN 10 ports, unless those ports are a member of both 1 AND 10. | ||
[[File:VLAN router as DHCP.png|File:VLAN router as DHCP.png]] | [[File:VLAN router as DHCP.png|File:VLAN router as DHCP.png]] | ||
| − | |||
| − | |||
=== PBX as DHCP server === | === PBX as DHCP server === | ||
Revision as of 20:11, 28 March 2019
vLANs
vLANs, or Virtual LANs, are a way to logically, rather than physically, segregate your network traffic. This can be done for multiple reasons, but primarily is done for security. Traffic from one vLAN cannot cross over to another without a static route existing on the router. Each individual port on a switch that supports vLANs can be configured as a member of one or more vLAN. The port itself can be configured as either an access port, which allows ONLY membership on a single vlan, and does not require setting up your device to support vLAN (tagging your traffic), or a trunk port, which can be a member of multiple vLANs simultaneously. vLAN traffic can either be untagged or tagged. These concepts will all be explained below.
Switch port types
Access
Access ports are intended for individual network devices, such as user PCs, phones, etc. These ports are members of a single vLAN, and ALL traffic received from the plugged in device is automatically considered to be part of that vLAN. This has the advantage of allowing devices to participate in a vLAN that do not natively support tagging. The disadvantage is that you cannot make use of multiple devices coming off of that single port that need to be on different vLANs, such as a phone on a voice vLAN, with a PC plugged into the phone's PC passthrough port, on the data vLAN.
Trunk
Trunk ports can carry multiple vLANs simultaneously. By default, they are generally configured to carry ALL vLANs, but can be restricted to specific ones in the switch vLAN port configuration section, depending on switch make and model. All trunk ports have a default vLAN membership, which is what vLAN untagged traffic is communicated on, and all other vLAN memberships must be tagged, so that the switch can know which vLAN to pass tagged packets to and from. If a device with a vLAN ID is connected to the port that does not match any of the port's membership IDs, it will not pass any packets tagged with that ID at all.
vLAN traffic
Untagged
All network traffic, unless otherwise specified, is untagged by default. This simply means it has no vLAN header at all, and lets the switch transmit this traffic on whatever the default vLAN that particular port is set to (see above in access and trunk sections).
Tagged
Packets with an optional vLAN header contain a VID (vLAN ID), which tells the switch what vLAN this packet belongs on. If the port is not a member of that particular vLAN, it will not pass the packet (in or out). This prevents someone from simply configuring a computer with the correct IP address information from accessing that network, if they are not plugged into a member port of the target vLAN, even if they do have the correct VID configured on their computer.
Setting Up your vLAN
The first thing you'll need to decide is what device you want to handle DHCP for the vLAN. If your router is capable of handling this, with separate DHCP services on it for each vLAN, or if you want the PBX itself to act as a DHCP server for the voice vLAN. If you use the PBX, it will also act as a gateway for the phones.
Router as DHCP server
- System=>VLAN
- Enable VLAN: DISABLED. What this does is enable/disable the pbx dhcp server and a virtual interface for the vlan. The switch port that the PBX is plugged into should be set up as a member of the intended voice vLAN, UNTAGGED, since the PBX will be sending untagged packets for voice traffic.
- PBX Setup=>Phone Global
- Apply VLAN Config to Phones: ENABLED
- Phone VLAN Enable: Enabled - this makes the phone's voice traffic tagged instead of untagged
- Phone VID: set this to the ID of the voice vLAN you have designated for the phone traffic
- Phone Priority: This is currently not used
- PC VLAN Enable: generally disabled, this is for the phone's PC passthrough port, if you want to tag PC traffic or leave it untagged
- PC VID: generally not used unless you're using a data vLAN, if so, set this according to what vLAN ID the computer's traffic should be tagged with. PC VLAN must be enabled for this to have any effect
- PC Priority: currently not used
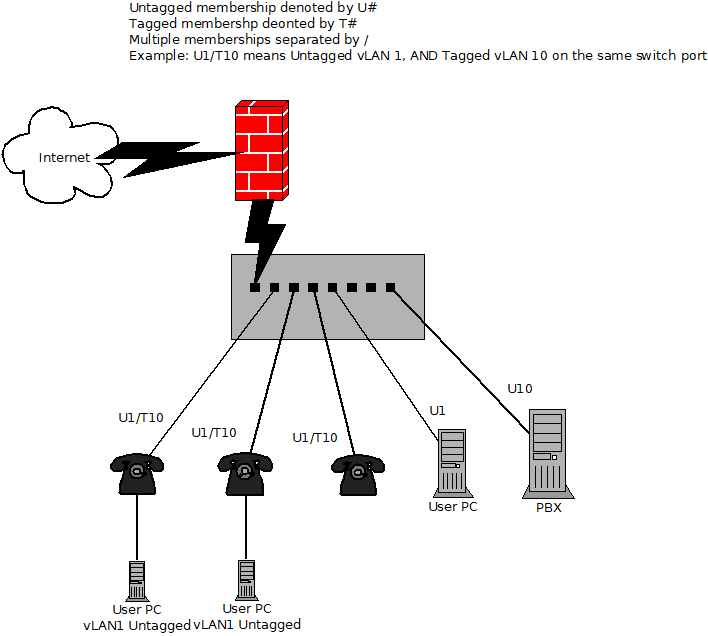
Switch setup: The port the PBX is going to be plugged into needs to be a member of the voice vLAN UNTAGGED (the pbx will be sending and receiving untagged traffic in this configuration). The ports that will have phones plugged into them will need to be members of the data vALN untagged, and the voice vLAN TAGGED, as the phone will be sending/receiving tagged packets, while the computer (if any), plugged into each phone, will be sending its data network traffic as UNtagged.
The ports that are members of vLAN 10, whether tagged or untagged, can communicate with each other. Ports NOT members of vLAN 10 at all can NOT communicate with vLAN 10 ports, unless those ports are a member of both 1 AND 10.
PBX as DHCP server
- System=>VLAN
- Enable VLAN: Enabled
- VLAN IP Address: This will be the IP address that the phones reach the PBX at. Leaving it default at 10.71.66.1 is generally fine, as you need it to be on a completely unique network range from the PBX's system=>networking IP range. Having this interface on the same network will cause the pbx to become unreachable.
- VLAN Subnet Mask: 255.255.255.0 will provide 254 useable addresses for your phone network. This is generally adequate.
- VID: 10 by default, but set this to whatever vlan ID is set in the switches for the voice vlan to use.
- Max DHCP Leases: This should be enough to cover the number of phones you anticipate having, but not be more than the number of addresses useable in the subnet mask, minus 1 address used by the pbx.
- DHCP Start Address and End Address: The range of your DHCP scope.
- PBX Setup=>Phone Global
- Apply VLAN Config to Phones: ENABLED
- Phone VLAN Enable: Enabled - this makes the phone's voice traffic tagged instead of untagged
- Phone VID: set this to the ID of the voice vLAN you have designated for the phone traffic
- Phone Priority: This is currently not used
- PC VLAN Enable: generally disabled, this is for the phone's PC passthrough port, if you want to tag PC traffic or leave it untagged
- PC VID: generally not used unless you're using a data vLAN, if so, set this according to what vLAN ID the computer's traffic should be tagged with. PC VLAN must be enabled for this to have any effect
- PC Priority: currently not used
Switch setup: The port the PBX is going to be plugged into needs to be a member of the data vLAN UNTAGGED and voice vLAN TAGGED (the pbx will be sending and receiving untagged traffic on the data vLAN to communicate with SIP trunks, for example, and all communication between the pbx and local phones will be in tagged packets on the voice vLAN, in this configuration). The ports that will have phones plugged into them will need to be members of the data vALN untagged, and the voice vLAN TAGGED, as the phone will be sending/receiving tagged packets, while the computer (if any), plugged into each phone, will be sending its data network traffic as UNtagged.